Socks 5 Proxy
What is Socks 5 Proxy - Intro
SOCKS 5 is a protocol defined in RFC 1928. Generally speaking, it is an improved version of SOCKS 4 which introduces, among other things, the support for IPv6 and UDP protocol. Moreover, the ways of authentication and authorization were changed, what improved the security of Proxy connections.
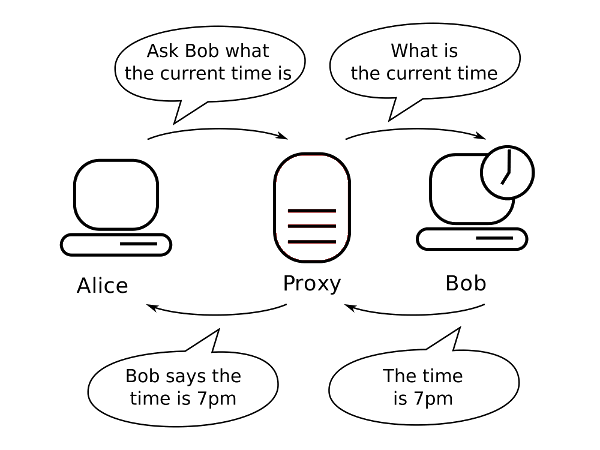
SOCKS is an intermediate protocol for TCP/IP applications that provides you with effective tools for safe communication. It consists of a part of the client implemented between the presentation layer and the transport layer and the server implemented in the application layer. This protocol allows for communication between two computers without a direct connection. This is a firewall that redirects host connections to another intermediate proxy server. The protocol maintains intermediate connections and exchanges data between hosts, authenticating and authorizing the task, activating the host on one of the server's pages to have full access to the hosts that are located on the other side of the SOCKS servers.
SOCKS 5 Proxy - benefits
1. Circumvent internet blocks
One of the main benefits of using the SOCKS 5 Proxy is that it provides you with an easy way to bypass the Internet blocks. In case when your IP was blacklisted by a particular website there is a strong chance to solve the problem by routing your traffic through this very protocol.
2. No limitations
Since the SOCKS 5 Proxy low-level protocol is much more secure and flexible than HTTP proxies, though it does not provide you with the high connection speed, it can practically work with any traffic and program. Hence, when using this improved version of SOCKS 4 Proxy there is no need to worry about running into protocol limitations.
3. Fast and reliable connection
The fact, that the SOCKS 5 Proxy servers are designed to use UDP protocol, provides stable connection and high-performance work. What makes the difference here is the application of User Data Protocol, which, unlike in the case of former proxies, allows to focus on the efficiency and speed. UDP, contrary to TCP, is not dedicated to intricate formatting data, it helps, however, to save time and get the better connection quality.
4. Improved overall performance
Since the SOCKS 5 Proxy does not rewrite data packet headers, the use of this protocol eliminates the risk of mislabeling or misrouting it. At the price of possible loss of a certain part of privacy (packet headers contain some personal information) you will surely benefit from lower likelihood of error occurrence and the performance improvement.
5. Better performance on P2P platforms
Considering that the SOCKS 5 Proxy transfers smaller packets of data, one of its most valuable assets is its faster download speed. This is, clearly, one of the reasons why this protocol is so highly popular in P2P sharing networks.
Why would I use a SOCKS 5 proxy?

The proxy server mediates between the recipient and the sender of the data packet. This allows you to hide your location from the recipient. This is quite important in the age of ubiquitous surveillance, when huge amounts of our personal data are collected by various websites. You can also bypass numerous regional blockades, imposed by operators or state institutions. SOCKS 5 Proxy is supported by many web browsers, FTP clients, SSH or even torrent clients. This allows for easy configuration and application of this server. You can find a lot of online guides on this topic along with some examples of configuration.
What is the difference between SOCKS 5 proxy and VPN?
Proxy-based solutions are faster, due to the lack of unnecessary encryption. It sometimes happens that the proxy server caches landing pages, resulting in a shorter response time and smaller data packets received. Also, most often SOCKS is cheaper than VPN. Another advantage of the proxy is the simplicity of configuration, as now many applications allow to install it very easily. Namely, all you have to do is enter more data in the right fields. Unlike VPN, using a proxy does not entail the need to install additional programs that interfere with the network settings of the operating system.
